by Jason Danner | Sep 13, 2017 | Security
Eight Bluetooth vulnerabilities have been identified and collectively called BlueBorne. These vulnerabilities are currently known to affect Windows, Linux, Android, Apple iOS and other smart devices. What this means The Blueborne vulnerabilities could allow a...

by Martin Danner | Jan 4, 2017 | Cloud Tips, Security, Tips & Techniques
To use a password manager safely, you need to know how to create a great master password. In my previous article, How To Manage Your Passwords, I discussed the importance of using strong and unique passwords. I also pointed out that a good password manager is the best...
by Jason Danner | Dec 2, 2016 | Security
What the heck is Gooligan? Googlian is a recently uncovered type of malware that stole the credentials to gain full access to users’ Google accounts after they installed a dodgy app on their Android phone. Currently there are more than 1 million Google accounts...

by Martin Danner | Dec 1, 2016 | Cloud Tips, Security, Tips & Techniques
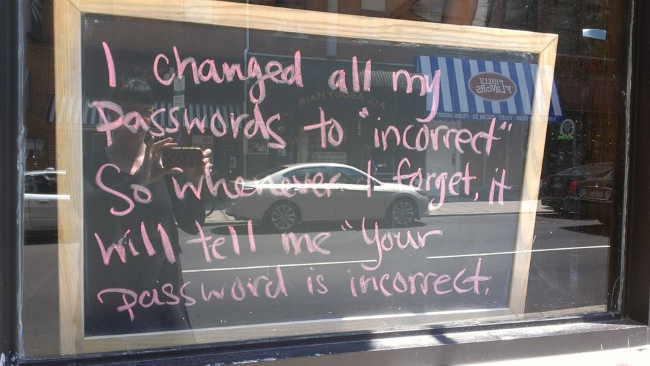
Passwords are a nightmare. Unfortunately, until something better comes along, you need them to protect pretty much everything you do online: from email, to Facebook to online banking. Conventional wisdom says to use a strong and unique password for each of your online...
by Jason Danner | Nov 22, 2016 | Security
Kiwicon is Christmas for the information security (infosec) community. This year, a jolly Metlstorm (Adam Boileau) guided us through two days of infosec bliss including: unique security talks, physical & digital security challenges, fire, lasers, alien abductions,...

by Martin Danner | Jul 12, 2016 | Security, Tips & Techniques
Earlier we explored the phenomenon of email phishing in an article called Does Your Email Smell Smell Phishy? Now there’s a new type of phishing attack called Whaling. Phishing involves carefully crafted email messages designed to trick you into clicking on...


Recent Comments